Providing Evidence
Since using application domain policy doesn't provide the desired results we start back from the initial .NET control. In this step evidence is explicitly provided and the .NET assembly for the control is loaded with this evidence - use the source code for review. The evidence is used as follows:
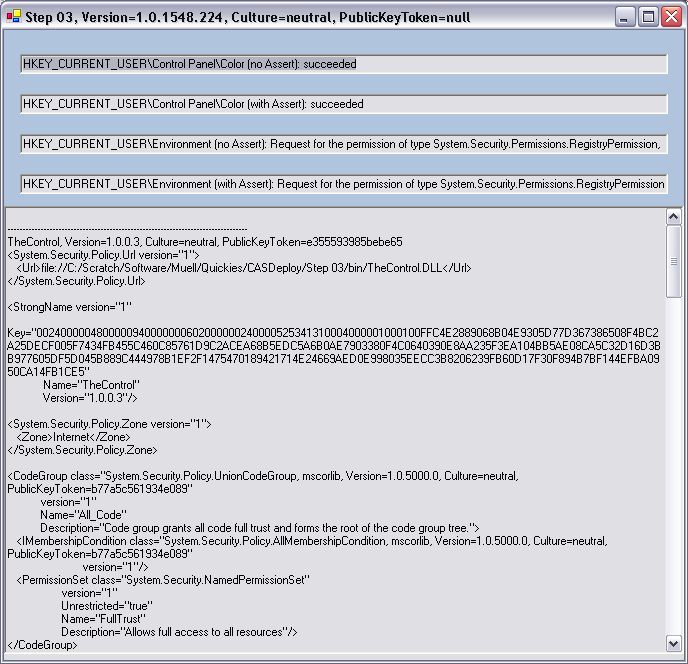
Providing a host evidence in such a way will ignore the MyComputer zone evidence which is calculated automatically and use the Internet zone evidence as required. All other evidence and especially the strong name and the related rights are preserved! The output is now like this:
But the result is not quite right since the .NET assembly is still allowed to access the registry without asserting the permission first. This is because the WinForms application is a fully trusted environment which automatically enables all rights granted to the .NET assembly. This can be corrected by initially restricting the run-time enviroment to the Internet zone - I think there are easier ways to do this as in the code shown below but it makes it's job:
This is very different from using the application domain policy since potentially a .NET assembly may assert for permissions which are not part of the Internet zone permission set if the related rights have been granted to it.
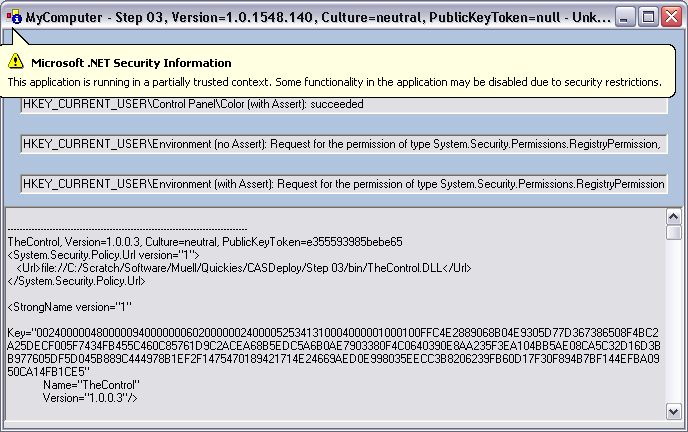
First of all the .NET run-time notifies the user that the current application runs with restricted rights:
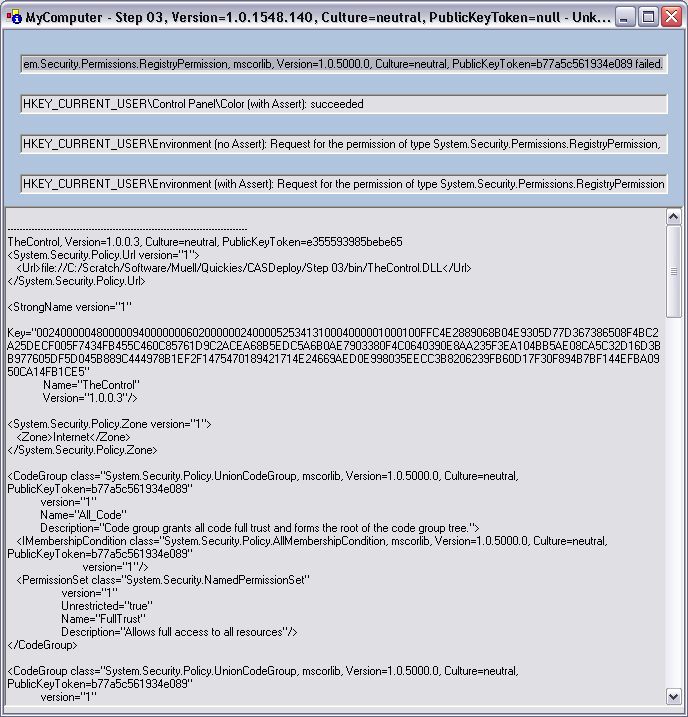
But when this is clicked away the control behaves in the expected way - the evidence log can be observed to verify the assignment of rights if needed:
For completeness I would like to show what happens if the .NET assembly is not loaded through the Internet zone evidence but the permit only feature is used:
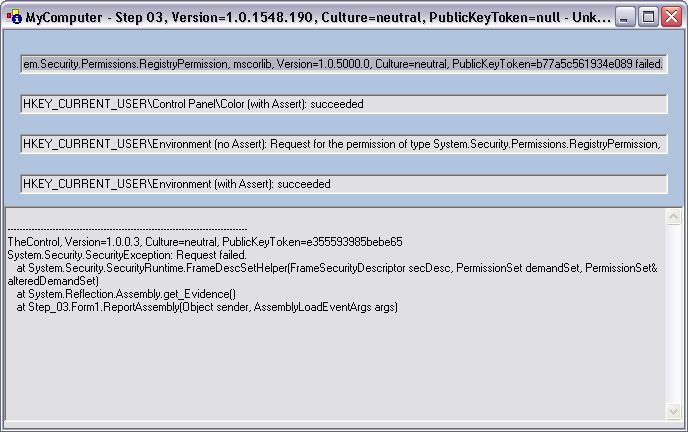
Since the .NET assembly is now fully trusted it can assert permissions for all registry keys - although a direct access with no assertion is not possible as required by the permit only. In addition it's no longer possible to report the evidence of the loaded .NET assembly. This is because the reporting method is called after security is locked down to the Internet zone and therefore the ControlEvidence permission is no longer activated - which could easily corrected by asserting the related permission since the WinForms application is fully trusted. Without this permission access to security information is prohibited.
Finally I added a last step to discuss the case where there are multiple .NET assemblies involved.